- Microsoft 2003 Compatibility Pack Download
- Microsoft Office 2003 Compatibility Pack For Mac Download
- Microsoft Office 2003 Compatibility Pack For Mac Torrent
- Microsoft Office 2003 Compatibility Pack For Mac Free
- Microsoft Office 2003 Compatibility Pack For Mac Windows 10
- Office 2003 Docx Compatibility Pack
If you work with any version of Excel 2000 through Excel 2003 for Windows and Excel for Mac 2011, you can download the Microsoft Office Compatibility Pack for Word, Excel, and PowerPoint File Formats from the Microsoft Download Center area on the Microsoft Web site (http://www.microsoft.com/download). The Microsoft Office Compatibility Pack has been updated to include SP2. Additionally, with the updated Compatibility Pack, if.DOCX or.DOCM files contain custom XML tags, those tags are removed when the file is opened in Word 2003.
- Microsoft Office Excel 2002 SP3, 2003 SP3, and 2007 SP1 and SP2; Office 2004 and 2008 for Mac; Open XML File Format Converter for Mac; Office Excel Viewer SP1 and SP2; and Office Compatibility Pack for Word, Excel, and PowerPoint 2007 File Formats SP1 and SP2 do not properly parse the Excel file format, which allows remote attackers to execute.
- Microsoft Office Compatibility Pack is an add-on for Microsoft Office 2000, Office XP and Office 2003 to open, edit and save Microsoft’s newer Word, Excel and Powerpoint formats that were introduced with Office 2007.
- By installing the Compatibility Pack in addition to Microsoft Office 2000, Office XP, or Office 2003, you will be able open, edit, and save files using the file formats new to Word, Excel, and PowerPoint 2007.
Microsoft Office 2008 for Mac applications: Word, Excel, PowerPoint and Entourage on Mac OS X 10.5 Leopard | |
| Developer(s) | Microsoft |
|---|---|
| Initial release | January 15, 2008; 12 years ago |
| Stable release | |
| Operating system | Mac OS X 10.4.9 or later |
| Type | Office suite |
| License | |
| Website | www.microsoft.com/mac/products/Office2008/default.mspx |
| System requirements[2] | |
|---|---|
| CPU | PowerPC G4 or G5 (500 MHz or faster) or any Intel processor |
| Operating system | Mac OS X10.4.9 or later |
| RAM | 512 MB |
| Free hard disk space | 1.5 GB |
| Optical drive | DVD-ROM (for local installation) |
| Notes | Unofficially runs on PowerPC G3 Macs (like the iMac G3 in Bondi Blue) and with less RAM |
Microsoft Office 2008 for Mac is a version of the Microsoft Officeproductivity suite for Mac OS X. It supersedes Office 2004 for Mac (which did not have Intel native code) and is the Mac OS X equivalent of Office 2007. Office 2008 was developed by Microsoft's Macintosh Business Unit and released on January 15, 2008. Office 2008 was followed by Microsoft Office for Mac 2011 released on October 26, 2010, requiring a Mac with an Intel processor and Mac OS version 10.5 or better. Office 2008 is also the last version to feature Entourage, which was replaced by Outlook in Office 2011. Microsoft stopped supporting Office 2008 on April 9, 2013.
Release[edit]
Office 2008 was originally slated for release in the second half of 2007; however, it was delayed until January 2008, purportedly to allow time to fix lingering bugs.[3] Office 2008 is the only version of Office for Mac supplied as a Universal Binary.
Unlike Office 2007 for Windows, Office 2008 was not offered as a public beta before its scheduled release date.[4]
Features[edit]
Office 2008 for Mac includes the same core programs currently included with Office 2004 for Mac: Entourage, Excel, PowerPoint and Word.
Mac-only features included are a publishing layout view, which offers functionality similar to Microsoft Publisher for Windows, a 'Ledger Sheet mode' in Excel to ease financial tasks, and a 'My Day' application offering a quick way to view the day's events.[5]
Office 2008 supports the new Office Open XML format, and defaults to saving all files in this format. On February 21, 2008 Geoff Price revealed that the format conversion update for Office 2004 would be delayed until June 2008 in order to provide the first update to Office 2008.[6]
Microsoft Visual Basic for Applications is not supported in this version.[7] As a result, such Excel add-ins dependent on VBA, such as Solver, have not been bundled in the current release.[8] In June 2008, Microsoft announced that it is exploring the idea of bringing some of the functionality of Solver back to Excel.[9] In late August 2008, Microsoft announced that a new Solver for Excel 2008 was available as a free download from Frontline Systems, original developers of the Excel Solver.[10][11] However, Excel 2008 also lacks other functionality, such as Pivot Chart functionality, which has long been a feature in the Windows version. In May 2008, Microsoft announced that VBA will be making a return in the next version of Microsoft Office for Mac.[12]AppleScript and the Open Scripting Architecture will still be supported.
Limitations[edit]
Office 2008 for Mac lacks feature parity with the Windows version. The lack of Visual Basic for Applications (VBA) support in Excel makes it impossible to use macros programmed in VBA. Microsoft's response is that adding VBA support in Xcode would have resulted in an additional two years added to the development cycle of Office 2008.[13] Other unsupported features include: OMML equations generated in Word 2007 for Windows,[14] Office 'Ribbon', Mini Toolbar, Live Preview, and an extensive list of features are unsupported such as equivalent SharePoint integration with the Windows version. Some features are missing on Excel 2008 for Mac, including: data filters (Data Bars, Top 10, Color-based, Icon-based), structured references, Excel tables, Table styles, a sort feature allowing more than three columns at once and more than one filter on a sort.
Benchmarks suggest that the original release of Office 2008 runs slower on Macs with PowerPC processors, and does not provide a significant speed bump for Macs with Intel processors.[15]
A using a program to remove application support files in unwanted languages), and which do not affect Office's operations, but which cause the updaters' installers to believe that the application is not valid for update. A small modification to the installer has been found an effective work-around (see reference).[18]
Another widespread problem reported after SP1 is that Office files will no longer open in Office applications when opened (double-clicked) from the Mac OS X Finder or launched from other applications such as an email attachment. The trigger for this problem is that Microsoft in SP1 unilaterally and without warning deprecated certain older Mac OS 'Type' codes such as 'WDBN' that some files may have, either because they are simply very old, or because some applications assign the older Type code when saving them to the disk. Users have seen the problem affect even relatively new Type codes, however, such as 'W6BN'. Microsoft is apparently looking into the problem, but it is unclear if they will reinstate the older Type codes, citing security concerns.[19]
Another problem with cross-platform compatibility is that images inserted into any Office application by using either cut and paste or drag and drop result in a file that does not display the inserted graphic when viewed on a Windows machine. Instead, the Windows user is told 'QuickTime and a TIFF (LZW) decompressor are needed to see this picture'. A user presented one solution as far back as December 2004.[20]
A further example of the lack of feature parity is the track changes function. Whereas users of Word 2003 or 2007 for Windows are able to choose freely between showing their changes in-line or as balloons in the right-hand margin,[21][22] choosing the former option in Word 2004 or Word 2008 for Mac OS also turns off all comment balloons; comments in this case are visible only in the Reviewing Pane or as popup boxes (i.e. upon mouseover).[23] This issue has not been resolved to date and is present in the latest version of Word for the Mac, namely Word 2011.[24]
The toolbox found in Office 2008 also has problems when the OS X feature Spaces is used: switching from one Space to another will cause elements of the Toolbox to get trapped on one Space until the Toolbox is closed and reopened. The only remedy for this problem is to currently disable Spaces, or at least refrain from using it whilst working in Office 2008.[25] Microsoft has acknowledged this problem and states that it is an architectural problem with the implementation of Spaces. Apple has been informed of the problem, according to Microsoft.[26] The problem appears to be caused by the fact that the Toolbox is Carbon-based.[citation needed] Using Microsoft Office with Mac OS X 10.6 Snow Leopard solves some of the problems.[26]
In addition, there is no support for right to left and bidirectional languages (such as Arabic, Hebrew, Persian, etc.) in Office 2008,[27][28] making it impossible to read or edit a right to left document in Word 2008 or PowerPoint 2008. Languages such as Thai are similarly not supported, although installing fonts can sometimes allow documents written in these languages to be displayed.
Moreover, Office 2008 proofing tools support only a limited number of languages (Danish, Dutch, English, Finnish, French, German, Italian, Japanese, Norwegian, Portuguese, Spanish, Swedish, and Swiss German).[29] Proofing tools for other languages failed to find their way to the installation pack, and are not offered by Microsoft commercially in the form of separately sold language packs. At the same time, Office applications are not integrated with the proofing tools native to Mac OS X 10.6 Leopard.
Microsoft Visio is not available for OS X. This means that any embedded Visio diagrams in other Office documents (e.g. Word) cannot be edited in Office on the Mac. Embedded Visio diagrams appear as a low-quality bitmap both in the WYSIWYG editor and upon printing the document on the Mac.
Editions[edit]
| Applications and services | Home & Student | Standard | Business Edition | Special Media Edition |
|---|---|---|---|---|
| Word | Yes | Yes | Yes | Yes |
| PowerPoint | Yes | Yes | Yes | Yes |
| Excel | Yes | Yes | Yes | Yes |
| Entourage | Yes | Yes | Yes | Yes |
| Exchange Server support | No | Yes | Yes | Yes |
| Automator Actions | No | Yes | Yes | Yes |
| Office Live and SharePoint support | No | No | Yes | No |
| Expression Media | No | No | No | Yes |
See also[edit]
References[edit]
- ^'Microsoft Support Lifecycle - Office 2008'. Microsoft. Retrieved February 10, 2018.
- ^'Microsoft Office 2008 for Mac Specs'. CNET. January 15, 2008. Retrieved January 5, 2017.
- ^'It's Coming: Mac BU Announces Intent to Deliver Office 2008 for Mac'. Microsoft. January 9, 2007. Archived from the original on October 11, 2007.
- ^'Microsoft Office 2008 for the Mac delayed until January 2008'. TUAW. August 2, 2007.
- ^'Microsoft starts testing Office 2008 for Mac'. Cnet. April 2, 2007. Archived from the original on September 28, 2007. Retrieved September 19, 2007.
- ^'MS Office Mac Discussion Board'. January 15, 2008.
- ^'Saying goodbye to Visual Basic'. August 8, 2006.
- ^'MS Office Mac Discussion Board'. January 15, 2008.
- ^'Excel 2008 and Solver'. June 26, 2008.
- ^'Solver For Excel 2008 Is Available'. August 29, 2008.
- ^'Solver is Back for Microsoft Excel 2008 on Macintosh'. August 29, 2008.
- ^'Microsoft Office Update, and Visual Basic for Applications to Return - Mac Rumors'. May 13, 2008.
- ^'MS Mactopia Blog'. March 13, 2008.
- ^Known issues in Word 2008 – Equations saved from Word 2007 for Windows do not appear in Word 2008 for Mac
- ^'MS Mactopia Blog'. March 13, 2008.
- ^'CambridgeSoft Website'.
- ^New installer for 12.0.1 (The Entourage Help Blog)
- ^MacFixit article: More Fixes for Problems InstallingArchived January 26, 2009, at the Wayback Machine
- ^http://www.microsoft.com/mac/help.mspx?target=0b9aa757-50ab-443b-8b0e-3a50ece1d5451033&clr=99-4-0
- ^'Archived copy'. Archived from the original on June 26, 2008. Retrieved June 30, 2008.CS1 maint: archived copy as title (link)
- ^'Archived copy'. Archived from the original on July 2, 2009. Retrieved July 9, 2009.CS1 maint: archived copy as title (link)
- ^'IT training – IT training – IT Services – Administrative and academic support divisions – Services and divisions – Staff and students – Home'. Ittraining.lse.ac.uk. May 7, 2010. Archived from the original on February 27, 2009. Retrieved May 30, 2010.
- ^[1][dead link]
- ^http://officeformac.com/ms/ProductForums/Word/11634/0
- ^Bugs & Fixes: Office 2008 and Leopard’s Spaces don’t mix, Macworld, December 8, 2008
- ^ abOffice 2008 for Mac and Mac OS X Spaces, Microsoft
- ^Help and How-To for Microsoft for Mac Office Products Mactopia
- ^Higgaion » It’s official: no RTL support in Microsoft Office 2008 for Mac
- ^Proofing tools that are available for each language
External links[edit]
- MacBU interview: Office 2008 Exchange Server support[permanent dead link]
Security Bulletin
Vulnerability in Microsoft Office Could Allow Remote Code Execution (2731879)
Word for mac change orientation of one page. Published: August 14, 2012 Updated: January 30, 2013
Version: 2.1
General Information
Executive Summary
This security update resolves one privately reported vulnerability in Microsoft Office. The vulnerability could allow remote code execution if a user opens a specially crafted file or embeds a specially crafted Computer Graphics Metafile (CGM) graphics file into an Office file. An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
This security update is rated Important for all supported editions of Microsoft Office 2007 and Microsoft Office 2010. For more information, see the subsection, Affected and Non-Affected Software, in this section.
The security update addresses the vulnerability by disabling the loading of CGM graphics files in Microsoft Office applications. For more information about the vulnerabilities, see the Frequently Asked Questions (FAQ) subsection for the specific vulnerability entry under the next section, Vulnerability Information.
Recommendation. Customers can configure automatic updating to check online for updates from Microsoft Update by using the Microsoft Update service. Customers who have automatic updating enabled and configured to check online for updates from Microsoft Update typically will not need to take any action because this security update will be downloaded and installed automatically. Customers who have not enabled automatic updating need to check for updates from Microsoft Update and install this update manually. For information about specific configuration options in automatic updating in supported editions of Windows XP and Windows Server 2003, see Microsoft Knowledge Base Article 294871. For information about automatic updating in supported editions of Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2, see Understanding Windows automatic updating.
For administrators and enterprise installations, or end users who want to install this security update manually, Microsoft recommends that customers apply the update at the earliest opportunity using update management software, or by checking for updates using the Microsoft Update service.
See also the section, Detection and Deployment Tools and Guidance, later in this bulletin.
Known Issues.Microsoft Knowledge Base Article 2731879 documents the currently known issues that customers may experience when installing this security update. The article also documents recommended solutions for these issues. When currently known issues and recommended solutions pertain only to specific releases of this software, this article provides links to further articles.
Affected and Non-Affected Software
The following software have been tested to determine which versions or editions are affected. Other versions or editions are either past their support life cycle or are not affected. To determine the support life cycle for your software version or edition, see Microsoft Support Lifecycle.
Affected Software
| Office Suite and Other Software | Maximum Security Impact | Aggregate Severity Rating | Updates Replaced |
|---|---|---|---|
| Microsoft Office 2007 Service Pack 2 (KB2596615) Microsoft Office 2007 Service Pack 2 (KB2596754) | Remote Code Execution | Important | KB2584063 in MS11-073 replaced by KB2596615 KB2288931 in MS10-105 replaced by KB2596754 |
| Microsoft Office 2007 Service Pack 3 (KB2596615) Microsoft Office 2007 Service Pack 3 (KB2596754) | Remote Code Execution | Important | None |
| Microsoft Office 2010 Service Pack 1 (32-bit editions) (KB2687501) Microsoft Office 2010 Service Pack 1 (32-bit editions) (KB2687510) | Remote Code Execution | Important | KB2584066 in MS11-073 replaced by KB2553260 or KB2687501 |
| Microsoft Office 2010 Service Pack 1 (64-bit editions) (KB2687501) Microsoft Office 2010 Service Pack 1 (64-bit editions) (KB2687510) | Remote Code Execution | Important | KB2584066 in MS11-073 replaced by KB2553260 or KB2687501 |
| Affected Software | CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 | Aggregate Severity Rating |
|---|---|---|
| Microsoft Office 2007 Service Pack 2 | Important Remote Code Execution | Important |
| Microsoft Office 2007 Service Pack 3 | Important Remote Code Execution | Important |
| Microsoft Office 2010 Service Pack 1 (32-bit editions) | Important Remote Code Execution | Important |
| Microsoft Office 2010 Service Pack 1 (64-bit editions) | Important Remote Code Execution | Important |
 CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 --------------------------------------------------------------- A remote code execution vulnerability exists in the way that Microsoft Office handles specially crafted Computer Graphics Metafile (CGM) graphics files. An attacker who successfully exploited this vulnerability could take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. To view this vulnerability as a standard entry in the Common Vulnerabilities and Exposures list, see [CVE-2012-2524](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2012-2524). #### Mitigating Factors for CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 Mitigation refers to a setting, common configuration, or general best-practice, existing in a default state, that could reduce the severity of exploitation of a vulnerability. The following mitigating factors may be helpful in your situation: - An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. - In a web-based attack scenario, an attacker could host a website that contains a specially crafted CGM file that is used to exploit this vulnerability. In addition, compromised websites and websites that accept or host user-provided content or advertisements could contain specially crafted content that could exploit this vulnerability. In all cases, however, an attacker would have no way to force users to visit these websites. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link in an email message or Instant Messenger message that takes users to the attacker’s website. - The vulnerability cannot be exploited automatically through email. For an attack to be successful a user must open an attachment that is sent in an email message. #### Workarounds for CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 Workaround refers to a setting or configuration change that does not correct the underlying vulnerability but would help block known attack vectors before you apply the update. Microsoft has tested the following workarounds and states in the discussion whether a workaround reduces functionality: - **Do not open Office files or embed CGM files that you receive from untrusted sources or that you receive unexpectedly from trusted sources** Do not open Office files or embed CGM files that you receive from untrusted sources or that you receive unexpectedly from trusted sources. This vulnerability could be exploited when a user opens a specially crafted file. #### FAQ for CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 **What is the scope of the vulnerability?** This is a remote code execution vulnerability. **What causes the vulnerability?** The vulnerability exists when Microsoft Office does not properly handle specially crafted CGM files causing corruption of memory that could lead to arbitrary code execution. **What might an attacker use the vulnerability to do?** An attacker who successfully exploited this vulnerability could run arbitrary code as the current user. If the current user is logged on with administrative user rights, an attacker could take complete control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. **How could an attacker exploit the vulnerability?** This vulnerability requires that a user open a specially crafted file with an affected version of Microsoft Office or insert a specially crafted CGM file into a document with an affected version of Microsoft Office. In an email attack scenario, an attacker could exploit the vulnerability by sending a specially crafted file to the user and by convincing the user to open the file. In a web-based attack scenario, an attacker would have to host a website that contains a specially crafted file that is used to attempt to exploit this vulnerability. In addition, compromised websites and websites that accept or host user-provided content could contain specially crafted content that could exploit this vulnerability. An attacker would have no way to force users to visit a specially crafted website. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link that takes them to the attacker's site. **What systems are primarily at risk from the vulnerability?** Systems where Microsoft Office is used, including workstations and terminal servers, are primarily at risk. Servers could be at more risk if administrators allow users to log on to servers and to run programs. However, best practices strongly discourage allowing this. **What does the update do?** The update addresses the vulnerability by disabling the loading of CGM graphics files in Microsoft Office applications. **When this security bulletin was issued, had this vulnerability been publicly disclosed?** No. Microsoft received information about this vulnerability through coordinated vulnerability disclosure. **When this security bulletin was issued, had Microsoft received any reports that this vulnerability was being exploited?** No. Microsoft had not received any information to indicate that this vulnerability had been publicly used to attack customers when this security bulletin was originally issued. ### Update Information Detection and Deployment Tools and Guidance ------------------------------------------- **Security Central** Manage the software and security updates you need to deploy to the servers, desktop, and mobile systems in your organization. For more information see the [TechNet Update Management Center](http://go.microsoft.com/fwlink/?linkid=69903). The [Microsoft TechNet Security website](http://go.microsoft.com/fwlink/?linkid=21132) provides additional information about security in Microsoft products. Security updates are available from [Microsoft Update](http://go.microsoft.com/fwlink/?linkid=40747) and [Windows Update](http://go.microsoft.com/fwlink/?linkid=21130). Security updates are also available from the [Microsoft Download Center](http://go.microsoft.com/fwlink/?linkid=21129). You can find them most easily by doing a keyword search for 'security update.' For customers of Microsoft Office for Mac, Microsoft AutoUpdate for Mac can help keep your Microsoft software up to date. For more information about using Microsoft AutoUpdate for Mac, see [Check for software updates automatically](http://mac2.microsoft.com/help/office/14/en-us/word/item/ffe35357-8f25-4df8-a0a3-c258526c64ea). Finally, security updates can be downloaded from the [Microsoft Update Catalog](http://go.microsoft.com/fwlink/?linkid=96155). The Microsoft Update Catalog provides a searchable catalog of content made available through Windows Update and Microsoft Update, including security updates, drivers and service packs. By searching using the security bulletin number (such as, 'MS12-001'), you can add all the applicable updates to your basket (including different languages for an update), and download to the folder of your choosing. For more information about the Microsoft Update Catalog, see the [Microsoft Update Catalog FAQ](http://go.microsoft.com/fwlink/?linkid=97900). **Detection and Deployment Guidance** Microsoft provides detection and deployment guidance for security updates. This guidance contains recommendations and information that can help IT professionals understand how to use various tools for detection and deployment of security updates. For more information, see [Microsoft Knowledge Base Article 961747](http://support.microsoft.com/kb/961747). **Microsoft Baseline Security Analyzer** Microsoft Baseline Security Analyzer (MBSA) lets administrators scan local and remote systems for missing security updates as well as common security misconfigurations. For more information, see [Microsoft Baseline Security Analyzer](http://go.microsoft.com/fwlink/?linkid=20567). The following table provides the MBSA detection summary for this security update. Software MBSA ---------------------------------------------------------------------------------- ------ Microsoft Office 2007 Service Pack 2 and Microsoft Office 2007 Service Pack 3 Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (32-bit editions) Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (64-bit editions) Yes **Note** For customers using legacy software not supported by the latest release of MBSA, Microsoft Update, and Windows Server Update Services, please see [Microsoft Baseline Security Analyzer](http://go.microsoft.com/fwlink/?linkid=20567) and reference the Legacy Product Support section on how to create comprehensive security update detection with legacy tools. **Windows Server Update Services** Windows Server Update Services (WSUS) enables information technology administrators to deploy the latest Microsoft product updates to computers that are running the Windows operating system. For more information about how to deploy security updates using Windows Server Update Services, see the TechNet article, [Windows Server Update Services](http://technet.microsoft.com/wsus/default.aspx). **Systems Management Server** The following table provides the SMS detection and deployment summary for this security update. Software SMS 2003 with ITMU System Center Configuration Manager ---------------------------------------------------------------------------------- -------------------- ------------------------------------- Microsoft Office 2007 Service Pack 2 and Microsoft Office 2007 Service Pack 3 Yes Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (32-bit editions) Yes Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (64-bit editions) Yes Yes **Note** Microsoft discontinued support for SMS 2.0 on April 12, 2011. For SMS 2003, Microsoft also discontinued support for the Security Update Inventory Tool (SUIT) on April 12, 2011. Customers are encouraged to upgrade to [System Center Configuration Manager](http://technet.microsoft.com/systemcenter/bb980621). For customers remaining on SMS 2003 Service Pack 3, the [Inventory Tool for Microsoft Updates](http://technet.microsoft.com/sms/bb676783.aspx) (ITMU) is also an option. For SMS 2003, the SMS 2003 Inventory Tool for Microsoft Updates (ITMU) can be used by SMS to detect security updates that are offered by [Microsoft Update](http://update.microsoft.com/microsoftupdate) and that are supported by [Windows Server Update Services](http://go.microsoft.com/fwlink/?linkid=50120). For more information about the SMS 2003 ITMU, see [SMS 2003 Inventory Tool for Microsoft Updates](http://technet.microsoft.com/sms/bb676783.aspx). For more information about SMS scanning tools, see [SMS 2003 Software Update Scanning Tools](http://technet.microsoft.com/sms/bb676786.aspx). See also [Downloads for Systems Management Server 2003](http://technet.microsoft.com/sms/bb676766.aspx). System Center Configuration Manager uses WSUS 3.0 for detection of updates. For more information, see [System Center](http://technet.microsoft.com/systemcenter/bb980621). For more detailed information, see [Microsoft Knowledge Base Article 910723](http://support.microsoft.com/kb/910723): Summary list of monthly detection and deployment guidance articles. **Note** If you have used an Administrative Installation Point (AIP) for deploying Office 2003, you may not be able to deploy the update using SMS if you have updated the AIP from the original baseline. For more information, see the **Office Administrative Installation Point** heading in this section. **Office Administrative Installation Point** If you installed your application from a server location, the server administrator must update the server location with the administrative update and deploy that update to your system. - For supported versions of Microsoft Office 2003, see [Creating an Administrative Installation Point](http://office.microsoft.com/en-us/ork2003/ha011401931033.aspx). For more information on how to change the source for a client computer from an updated administrative installation point to an Office 2003 original baseline source or Service Pack 3 (SP3), see [Microsoft Knowledge Base Article 902349](http://support.microsoft.com/kb/902349). **Note** If you plan to manage software updates centrally from an updated administrative image, you can find more information in the article, [Distributing Office 2003 Product Updates](http://office.microsoft.com/en-us/ork2003/ha011402381033.aspx?pid=ch011480761033). - For creating a network installation point for supported versions of Microsoft Office, see [Create a network installation point for Microsoft Office](http://technet.microsoft.com/library/cc179063.aspx). **Note** If you plan to manage security updates centrally, use Windows Server Update Services. For more information about how to deploy security updates for Microsoft Office, see the [Windows Server Update Services website](http://technet.microsoft.com/wsus/default.aspx). **Update Compatibility Evaluator and Application Compatibility Toolkit** Updates often write to the same files and registry settings required for your applications to run. This can trigger incompatibilities and increase the time it takes to deploy security updates. You can streamline testing and validating Windows updates against installed applications with the [Update Compatibility Evaluator](http://technet.microsoft.com/library/cc749197) components included with [Application Compatibility Toolkit](https://www.microsoft.com/download/details.aspx?familyid=24da89e9-b581-47b0-b45e-492dd6da2971). The Application Compatibility Toolkit (ACT) contains the necessary tools and documentation to evaluate and mitigate application compatibility issues before deploying Windows Vista, a Windows Update, a Microsoft Security Update, or a new version of Windows Internet Explorer in your environment. Security Update Deployment -------------------------- **Affected Software** For information about the specific security update for your affected software, click the appropriate link: #### Microsoft Office 2007 (all editions) **Reference Table** The following table contains the security update information for this software. You can find additional information in the subsection, **Deployment Information**, in this section.
CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 --------------------------------------------------------------- A remote code execution vulnerability exists in the way that Microsoft Office handles specially crafted Computer Graphics Metafile (CGM) graphics files. An attacker who successfully exploited this vulnerability could take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. To view this vulnerability as a standard entry in the Common Vulnerabilities and Exposures list, see [CVE-2012-2524](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2012-2524). #### Mitigating Factors for CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 Mitigation refers to a setting, common configuration, or general best-practice, existing in a default state, that could reduce the severity of exploitation of a vulnerability. The following mitigating factors may be helpful in your situation: - An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. - In a web-based attack scenario, an attacker could host a website that contains a specially crafted CGM file that is used to exploit this vulnerability. In addition, compromised websites and websites that accept or host user-provided content or advertisements could contain specially crafted content that could exploit this vulnerability. In all cases, however, an attacker would have no way to force users to visit these websites. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link in an email message or Instant Messenger message that takes users to the attacker’s website. - The vulnerability cannot be exploited automatically through email. For an attack to be successful a user must open an attachment that is sent in an email message. #### Workarounds for CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 Workaround refers to a setting or configuration change that does not correct the underlying vulnerability but would help block known attack vectors before you apply the update. Microsoft has tested the following workarounds and states in the discussion whether a workaround reduces functionality: - **Do not open Office files or embed CGM files that you receive from untrusted sources or that you receive unexpectedly from trusted sources** Do not open Office files or embed CGM files that you receive from untrusted sources or that you receive unexpectedly from trusted sources. This vulnerability could be exploited when a user opens a specially crafted file. #### FAQ for CGM File Format Memory Corruption Vulnerability - CVE-2012-2524 **What is the scope of the vulnerability?** This is a remote code execution vulnerability. **What causes the vulnerability?** The vulnerability exists when Microsoft Office does not properly handle specially crafted CGM files causing corruption of memory that could lead to arbitrary code execution. **What might an attacker use the vulnerability to do?** An attacker who successfully exploited this vulnerability could run arbitrary code as the current user. If the current user is logged on with administrative user rights, an attacker could take complete control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. **How could an attacker exploit the vulnerability?** This vulnerability requires that a user open a specially crafted file with an affected version of Microsoft Office or insert a specially crafted CGM file into a document with an affected version of Microsoft Office. In an email attack scenario, an attacker could exploit the vulnerability by sending a specially crafted file to the user and by convincing the user to open the file. In a web-based attack scenario, an attacker would have to host a website that contains a specially crafted file that is used to attempt to exploit this vulnerability. In addition, compromised websites and websites that accept or host user-provided content could contain specially crafted content that could exploit this vulnerability. An attacker would have no way to force users to visit a specially crafted website. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link that takes them to the attacker's site. **What systems are primarily at risk from the vulnerability?** Systems where Microsoft Office is used, including workstations and terminal servers, are primarily at risk. Servers could be at more risk if administrators allow users to log on to servers and to run programs. However, best practices strongly discourage allowing this. **What does the update do?** The update addresses the vulnerability by disabling the loading of CGM graphics files in Microsoft Office applications. **When this security bulletin was issued, had this vulnerability been publicly disclosed?** No. Microsoft received information about this vulnerability through coordinated vulnerability disclosure. **When this security bulletin was issued, had Microsoft received any reports that this vulnerability was being exploited?** No. Microsoft had not received any information to indicate that this vulnerability had been publicly used to attack customers when this security bulletin was originally issued. ### Update Information Detection and Deployment Tools and Guidance ------------------------------------------- **Security Central** Manage the software and security updates you need to deploy to the servers, desktop, and mobile systems in your organization. For more information see the [TechNet Update Management Center](http://go.microsoft.com/fwlink/?linkid=69903). The [Microsoft TechNet Security website](http://go.microsoft.com/fwlink/?linkid=21132) provides additional information about security in Microsoft products. Security updates are available from [Microsoft Update](http://go.microsoft.com/fwlink/?linkid=40747) and [Windows Update](http://go.microsoft.com/fwlink/?linkid=21130). Security updates are also available from the [Microsoft Download Center](http://go.microsoft.com/fwlink/?linkid=21129). You can find them most easily by doing a keyword search for 'security update.' For customers of Microsoft Office for Mac, Microsoft AutoUpdate for Mac can help keep your Microsoft software up to date. For more information about using Microsoft AutoUpdate for Mac, see [Check for software updates automatically](http://mac2.microsoft.com/help/office/14/en-us/word/item/ffe35357-8f25-4df8-a0a3-c258526c64ea). Finally, security updates can be downloaded from the [Microsoft Update Catalog](http://go.microsoft.com/fwlink/?linkid=96155). The Microsoft Update Catalog provides a searchable catalog of content made available through Windows Update and Microsoft Update, including security updates, drivers and service packs. By searching using the security bulletin number (such as, 'MS12-001'), you can add all the applicable updates to your basket (including different languages for an update), and download to the folder of your choosing. For more information about the Microsoft Update Catalog, see the [Microsoft Update Catalog FAQ](http://go.microsoft.com/fwlink/?linkid=97900). **Detection and Deployment Guidance** Microsoft provides detection and deployment guidance for security updates. This guidance contains recommendations and information that can help IT professionals understand how to use various tools for detection and deployment of security updates. For more information, see [Microsoft Knowledge Base Article 961747](http://support.microsoft.com/kb/961747). **Microsoft Baseline Security Analyzer** Microsoft Baseline Security Analyzer (MBSA) lets administrators scan local and remote systems for missing security updates as well as common security misconfigurations. For more information, see [Microsoft Baseline Security Analyzer](http://go.microsoft.com/fwlink/?linkid=20567). The following table provides the MBSA detection summary for this security update. Software MBSA ---------------------------------------------------------------------------------- ------ Microsoft Office 2007 Service Pack 2 and Microsoft Office 2007 Service Pack 3 Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (32-bit editions) Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (64-bit editions) Yes **Note** For customers using legacy software not supported by the latest release of MBSA, Microsoft Update, and Windows Server Update Services, please see [Microsoft Baseline Security Analyzer](http://go.microsoft.com/fwlink/?linkid=20567) and reference the Legacy Product Support section on how to create comprehensive security update detection with legacy tools. **Windows Server Update Services** Windows Server Update Services (WSUS) enables information technology administrators to deploy the latest Microsoft product updates to computers that are running the Windows operating system. For more information about how to deploy security updates using Windows Server Update Services, see the TechNet article, [Windows Server Update Services](http://technet.microsoft.com/wsus/default.aspx). **Systems Management Server** The following table provides the SMS detection and deployment summary for this security update. Software SMS 2003 with ITMU System Center Configuration Manager ---------------------------------------------------------------------------------- -------------------- ------------------------------------- Microsoft Office 2007 Service Pack 2 and Microsoft Office 2007 Service Pack 3 Yes Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (32-bit editions) Yes Yes Microsoft Office 2010 and Microsoft Office 2010 Service Pack 1 (64-bit editions) Yes Yes **Note** Microsoft discontinued support for SMS 2.0 on April 12, 2011. For SMS 2003, Microsoft also discontinued support for the Security Update Inventory Tool (SUIT) on April 12, 2011. Customers are encouraged to upgrade to [System Center Configuration Manager](http://technet.microsoft.com/systemcenter/bb980621). For customers remaining on SMS 2003 Service Pack 3, the [Inventory Tool for Microsoft Updates](http://technet.microsoft.com/sms/bb676783.aspx) (ITMU) is also an option. For SMS 2003, the SMS 2003 Inventory Tool for Microsoft Updates (ITMU) can be used by SMS to detect security updates that are offered by [Microsoft Update](http://update.microsoft.com/microsoftupdate) and that are supported by [Windows Server Update Services](http://go.microsoft.com/fwlink/?linkid=50120). For more information about the SMS 2003 ITMU, see [SMS 2003 Inventory Tool for Microsoft Updates](http://technet.microsoft.com/sms/bb676783.aspx). For more information about SMS scanning tools, see [SMS 2003 Software Update Scanning Tools](http://technet.microsoft.com/sms/bb676786.aspx). See also [Downloads for Systems Management Server 2003](http://technet.microsoft.com/sms/bb676766.aspx). System Center Configuration Manager uses WSUS 3.0 for detection of updates. For more information, see [System Center](http://technet.microsoft.com/systemcenter/bb980621). For more detailed information, see [Microsoft Knowledge Base Article 910723](http://support.microsoft.com/kb/910723): Summary list of monthly detection and deployment guidance articles. **Note** If you have used an Administrative Installation Point (AIP) for deploying Office 2003, you may not be able to deploy the update using SMS if you have updated the AIP from the original baseline. For more information, see the **Office Administrative Installation Point** heading in this section. **Office Administrative Installation Point** If you installed your application from a server location, the server administrator must update the server location with the administrative update and deploy that update to your system. - For supported versions of Microsoft Office 2003, see [Creating an Administrative Installation Point](http://office.microsoft.com/en-us/ork2003/ha011401931033.aspx). For more information on how to change the source for a client computer from an updated administrative installation point to an Office 2003 original baseline source or Service Pack 3 (SP3), see [Microsoft Knowledge Base Article 902349](http://support.microsoft.com/kb/902349). **Note** If you plan to manage software updates centrally from an updated administrative image, you can find more information in the article, [Distributing Office 2003 Product Updates](http://office.microsoft.com/en-us/ork2003/ha011402381033.aspx?pid=ch011480761033). - For creating a network installation point for supported versions of Microsoft Office, see [Create a network installation point for Microsoft Office](http://technet.microsoft.com/library/cc179063.aspx). **Note** If you plan to manage security updates centrally, use Windows Server Update Services. For more information about how to deploy security updates for Microsoft Office, see the [Windows Server Update Services website](http://technet.microsoft.com/wsus/default.aspx). **Update Compatibility Evaluator and Application Compatibility Toolkit** Updates often write to the same files and registry settings required for your applications to run. This can trigger incompatibilities and increase the time it takes to deploy security updates. You can streamline testing and validating Windows updates against installed applications with the [Update Compatibility Evaluator](http://technet.microsoft.com/library/cc749197) components included with [Application Compatibility Toolkit](https://www.microsoft.com/download/details.aspx?familyid=24da89e9-b581-47b0-b45e-492dd6da2971). The Application Compatibility Toolkit (ACT) contains the necessary tools and documentation to evaluate and mitigate application compatibility issues before deploying Windows Vista, a Windows Update, a Microsoft Security Update, or a new version of Windows Internet Explorer in your environment. Security Update Deployment -------------------------- **Affected Software** For information about the specific security update for your affected software, click the appropriate link: #### Microsoft Office 2007 (all editions) **Reference Table** The following table contains the security update information for this software. You can find additional information in the subsection, **Deployment Information**, in this section.| Inclusion in Future Service Packs | The update for this issue will be included in a future service pack or update rollup |
| Deployment | |
| Installing without user intervention | For supported editions of Microsoft Office 2007 software: mso2007-kb2596615-fullfile-x86-glb.exe /passive msconv972007-kb2596754-fullfile-x86-glb.exe /passive |
| Installing without restarting | For supported editions of Microsoft Office 2007 software: mso2007-kb2596615-fullfile-x86-glb.exe /norestart msconv972007-kb2596754-fullfile-x86-glb.exe /norestart |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. |
| Restart Requirement | |
| Restart required? | In some cases, this update does not require a restart. If the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to restart. To help reduce the chance that a restart will be required, stop all affected services and close all applications that may use the affected files prior to installing the security update. For more information about the reasons why you may be prompted to restart, see Microsoft Knowledge Base Article 887012. |
| HotPatching | Not applicable |
| Removal Information | Use Add or Remove Programs item in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2596615 and Microsoft Knowledge Base Article 2596754 |
| Registry Key Verification | Not applicable |
Supported Security Update Installation Switches
| Switch | Description |
|---|---|
| /? or /help | Displays usage dialog. |
| /passive | Specifies passive mode. Requires no user interaction; users see basic progress dialogs but cannot cancel. |
| /quiet | Specifies quiet mode, or suppresses prompts, when files are being extracted. |
| /norestart | Suppresses restarting the system if the update requires a restart. |
| /forcerestart | Automatically restarts the system after applying the update, regardless of whether the update requires the restart. |
| /extract | Extracts the files without installing them. You are prompted for a target folder. |
| /extract:<path> | Overrides the install command that is defined by author. Specifies the path and name of the Setup.inf or .exe file. |
| /lang:<LCID> | Forces the use of a specific language, when the update package supports that language. |
| /log:<log file> | Enables logging, by both Vnox and Installer, during the update installation. |
Note You can combine these switches into one command. For backward compatibility, the security update also supports many of the setup switches that the earlier version of the Setup program uses. For more information about the supported installation switches, see Microsoft Knowledge Base Article 262841.
Removing the Update
To remove this security update, use the Add or Remove Programs item in Control Panel.
Note When you remove this update, you may be prompted to insert the 2007 Microsoft Office CD in the CD drive. Additionally, you may not have the option to uninstall the update from the Add or Remove Programs item in Control Panel. There are several possible causes for this issue. For more information about the removal, see Microsoft Knowledge Base Article 903771.
Verifying that the Update Has Been Applied
Microsoft Baseline Security Analyzer
To verify that a security update has been applied to an affected system, you may be able to use the Microsoft Baseline Security Analyzer (MBSA) tool. See the section, Detection and Deployment Tools and Guidance, earlier in this bulletin for more information.File Version Verification
Because there are several editions of Microsoft Windows, the following steps may be different on your system. If they are, see your product documentation to complete these steps.- Click Start and then enter an update file name in the Start Search box.
- When the file appears under Programs, right-click the file name and click Properties.
- On the General tab, compare the file size with the file information tables provided in the bulletin KB article.
Note Depending on the edition of the operating system, or the programs that are installed on your system, some files that are listed in the file information table may not be installed. - You can also click the Details tab and compare information, such as file version and date modified, with the file information tables provided in the bulletin KB article.
Note Attributes other than the file version may change during installation. Comparing other file attributes to the information in the file information table is not a supported method of verifying that the update has been applied. Also, in certain cases, files may be renamed during installation. If the file or version information is not present, use one of the other available methods to verify update installation. - Finally, you can also click the Previous Versions tab and compare file information for the previous version of the file with the file information for the new, or updated, version of the file.
Microsoft Office 2010 (all editions)
Reference Table
The following table contains the security update information for this software. You can find additional information in the subsection, Deployment Information, in this section.
Microsoft 2003 Compatibility Pack Download
| Inclusion in Future Service Packs | The update for this issue will be included in a future service pack or update rollup |
| Deployment | |
| Installing without user intervention | For Microsoft Office 2010 (32-bit editions) software: mso2010-kb2687501-fullfile-x86-glb.exe /passive msconv972010-kb2687510-fullfile-x86-glb.exe /norestart |
| For Microsoft Office 2010 (64-bit editions) software: mso2010-kb2687501-fullfile-x64-glb.exe /passive msconv972010-kb2687510-fullfile-x64-glb.exe /passive | |
| Installing without restarting | For Microsoft Office 2010 (32-bit editions) software: mso2010-kb2687501-fullfile-x86-glb.exe /norestart msconv972010-kb2687510-fullfile-x86-glb.exe /norestart |
| For Microsoft Office 2010 (64-bit editions) software: mso2010-kb2687501-fullfile-x64-glb.exe /norestart msconv972010-kb2687510-fullfile-x64-glb.exe /norestart | |
| Update log file | Not applicable |
| Further information | For detection and deployment, see the earlier section, Detection and Deployment Tools and Guidance. |
| Restart Requirement | |
| Restart required? | In some cases, this update does not require a restart. If the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to restart. To help reduce the chance that a restart will be required, stop all affected services and close all applications that may use the affected files prior to installing the security update. For more information about the reasons why you may be prompted to restart, see Microsoft Knowledge Base Article 887012. |
| HotPatching | Not applicable |
| Removal Information | Use Add or Remove Programs item in Control Panel. |
| File Information | See Microsoft Knowledge Base Article 2687501 and Microsoft Knowledge Base Article 2687510 |
| Registry Key Verification | Not applicable |
Supported Security Update Installation Switches
| Switch | Description |
|---|---|
| /? or /help | Displays usage dialog. |
| /passive | Specifies passive mode. Requires no user interaction; users see basic progress dialogs but cannot cancel. |
| /quiet | Specifies quiet mode, or suppresses prompts, when files are being extracted. |
| /norestart | Suppresses restarting the system if the update requires a restart. |
| /forcerestart | Automatically restarts the system after applying the update, regardless of whether the update requires the restart. |
| /extract | Extracts the files without installing them. You are prompted for a target folder. |
| /extract:<path> | Overrides the install command that is defined by author. Specifies the path and name of the Setup.inf or .exe file. |
| /lang:<LCID> | Forces the use of a specific language, when the update package supports that language. |
| /log:<log file> | Enables logging, by both Vnox and Installer, during the update installation. |
Microsoft Office 2003 Compatibility Pack For Mac Download
Note You can combine these switches into one command. For backward compatibility, the security update also supports many of the setup switches that the earlier version of the Setup program uses. For more information about the supported installation switches, see Microsoft Knowledge Base Article 262841.
Removing the Update
To remove this security update, use the Add or Remove Programs item in Control Panel.
Note When you remove this update, you may be prompted to insert the 2007 Microsoft Office CD in the CD drive. Additionally, you may not have the option to uninstall the update from the Add or Remove Programs item in Control Panel. There are several possible causes for this issue. For more information about the removal, see Microsoft Knowledge Base Article 903771.
Verifying that the Update Has Been Applied
Microsoft Baseline Security Analyzer
To verify that a security update has been applied to an affected system, you may be able to use the Microsoft Baseline Security Analyzer (MBSA) tool. See the section, Detection and Deployment Tools and Guidance, earlier in this bulletin for more information.File Version Verification
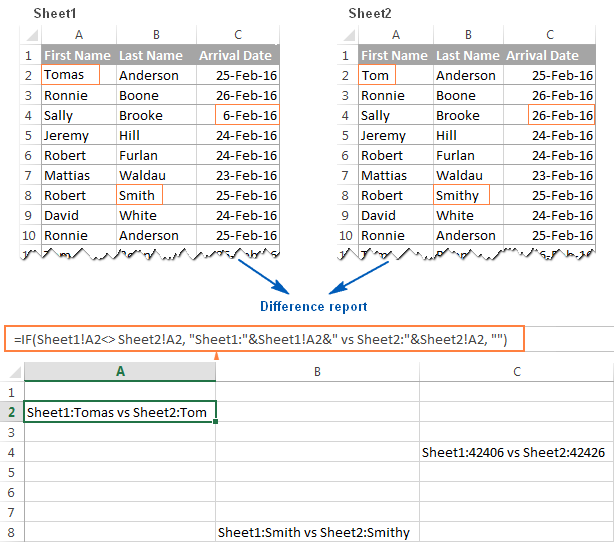
Because there are several editions of Microsoft Windows, the following steps may be different on your system. If they are, see your product documentation to complete these steps.Among your options: you can check them manually, you can use a formula or, if the two columns are in different worksheets, you can view them side by side. There are several different ways to compare data between two columns in Microsoft Excel.
- Click Start and then enter an update file name in the Start Search box.
- When the file appears under Programs, right-click the file name and click Properties.
- On the General tab, compare the file size with the file information tables provided in the bulletin KB article.
Note Depending on the edition of the operating system, or the programs that are installed on your system, some files that are listed in the file information table may not be installed. - You can also click the Details tab and compare information, such as file version and date modified, with the file information tables provided in the bulletin KB article.
Note Attributes other than the file version may change during installation. Comparing other file attributes to the information in the file information table is not a supported method of verifying that the update has been applied. Also, in certain cases, files may be renamed during installation. If the file or version information is not present, use one of the other available methods to verify update installation. - Finally, you can also click the Previous Versions tab and compare file information for the previous version of the file with the file information for the new, or updated, version of the file.
Other Information
Acknowledgments
Microsoft thanks the following for working with us to help protect customers:
- Andrei Costin for reporting the CGM File Format Memory Corruption Vulnerability (CVE-2012-2524)
Microsoft Active Protections Program (MAPP)
To improve security protections for customers, Microsoft provides vulnerability information to major security software providers in advance of each monthly security update release. Security software providers can then use this vulnerability information to provide updated protections to customers via their security software or devices, such as antivirus, network-based intrusion detection systems, or host-based intrusion prevention systems. To determine whether active protections are available from security software providers, please go to the active protections websites provided by program partners, listed in Microsoft Active Protections Program (MAPP) Partners.
Support
How to obtain help and support for this security update
Microsoft Office 2003 Compatibility Pack For Mac Torrent
- Help installing updates: Support for Microsoft Update
- Security solutions for IT professionals: TechNet Security Troubleshooting and Support
- Help protect your computer that is running Windows from viruses and malware: Virus Solution and Security Center
- Local support according to your country: International Support
Disclaimer
The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
Microsoft Office 2003 Compatibility Pack For Mac Free
Revisions
Microsoft Office 2003 Compatibility Pack For Mac Windows 10
- V1.0 (August 14, 2012): Bulletin published.
- V2.0 (December 11, 2012): Rereleased bulletin to replace the KB2553260 and KB2589322 updates with the KB2687501 and KB2687510 updates respectively for Microsoft Office 2010 Service Pack 1. See the update FAQ for details.
- V2.1 (January 30, 2013): Clarified that customers with the KB2553260 and KB2589322 updates will be offered the KB2687501 and KB2687510 updates respectively for Microsoft Office 2010 Service Pack 1. See the update FAQ for details.
Office 2003 Docx Compatibility Pack
Built at 2014-04-18T13:49:36Z-07:00